Trip report: July 2025 Schloss Dagstuhl seminar on 'Building Privacy-Preserving Technologies of Societal Impact' (Wadern, Germany)
Last week Mark Abspoel and I participated in Dagstuhl Seminar 25312, titled “Building Privacy-Preserving Technologies of Societal Impact.” Organised by Marina Blanton (University of Buffalo, NY, USA) and Liina Kamm (Cybernetica, Estonia), twenty-eight experts gathered last week in Schloss Dagstuhl to exchange information about impactful applications of Secure Multi-Party Computation (MPC) and other Privacy-Enhancing Technologies (PETs), and discuss strategies for accelerating the adoption of these technologies.
Schloss Dagstuhl
In case you are unfamiliar, Schloss Dagstuhl is a seminar facility for computer science, housed in an 18th-century castle in Wadern, which is in midwest Germany, near the cities of Trier and Saarbrücken. The invitation-based Dagstuhl Seminars “focus on the exchange and development of ideas” and “promote personal interaction and open discussion.” Beyond the delicious regular meals, participants are spoilt with daily pastry served around tea time in Dagstuhl’s lawn, as well as with a cheese platter served at 8pm sharp, to be enjoyed together with other participants in the castle’s wine cellar…
The Seminar
The seminar ran from Monday morning (July 28th) to Friday noon (Aug 1st), and kicked off with personal introductions of the 28 seminar participants. The group consisted of 17 academics, 6 people from industry, 4 from research institutes / non-profits, and 1 from the public sector. There was an interesting mix of expertise in the room, like privacy researchers, cryptographers, MPC engineers, database experts and a medical professional.
The biggest part of the seminar agenda was filled with talks given by the participants. Monday and Tuesday were reserved for “MPC & PET applications of societal impact,” Wednesday for “MPC engineering” and Thursday for “PETs and user studies.” The program was interspersed with several discussion slots about PET-related issues, for example regarding raising awareness among stakeholders of the capabilities and benefits of PETs, and identifying levers to stimulate their adoption.
Let me highlight some talks from the seminar.
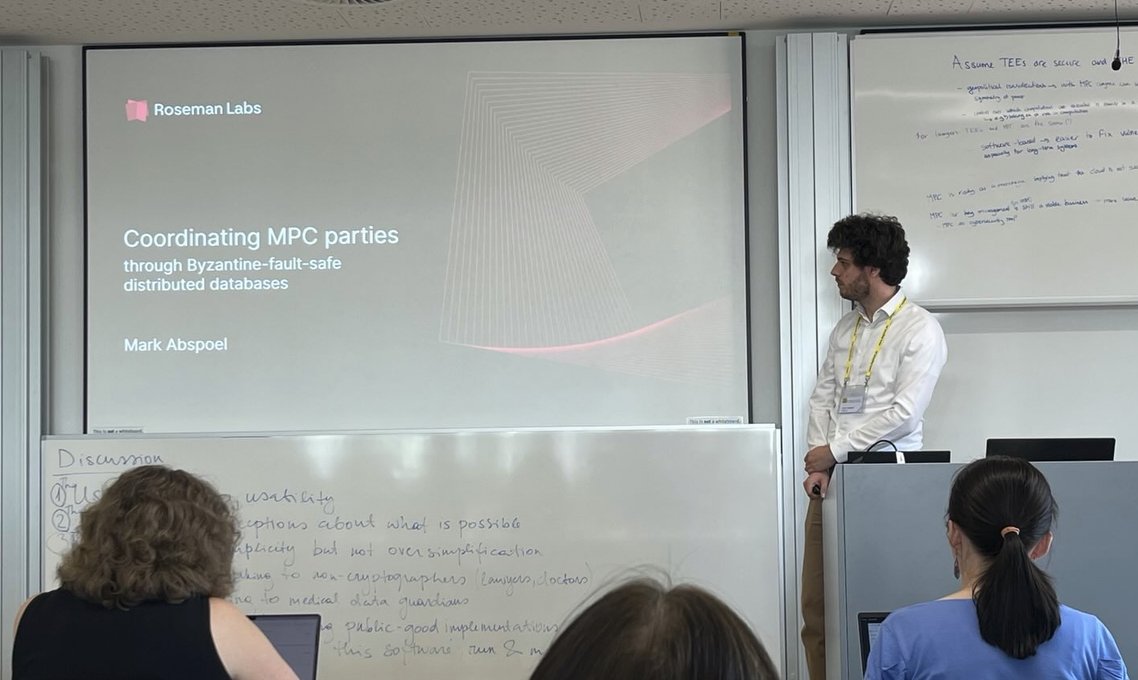
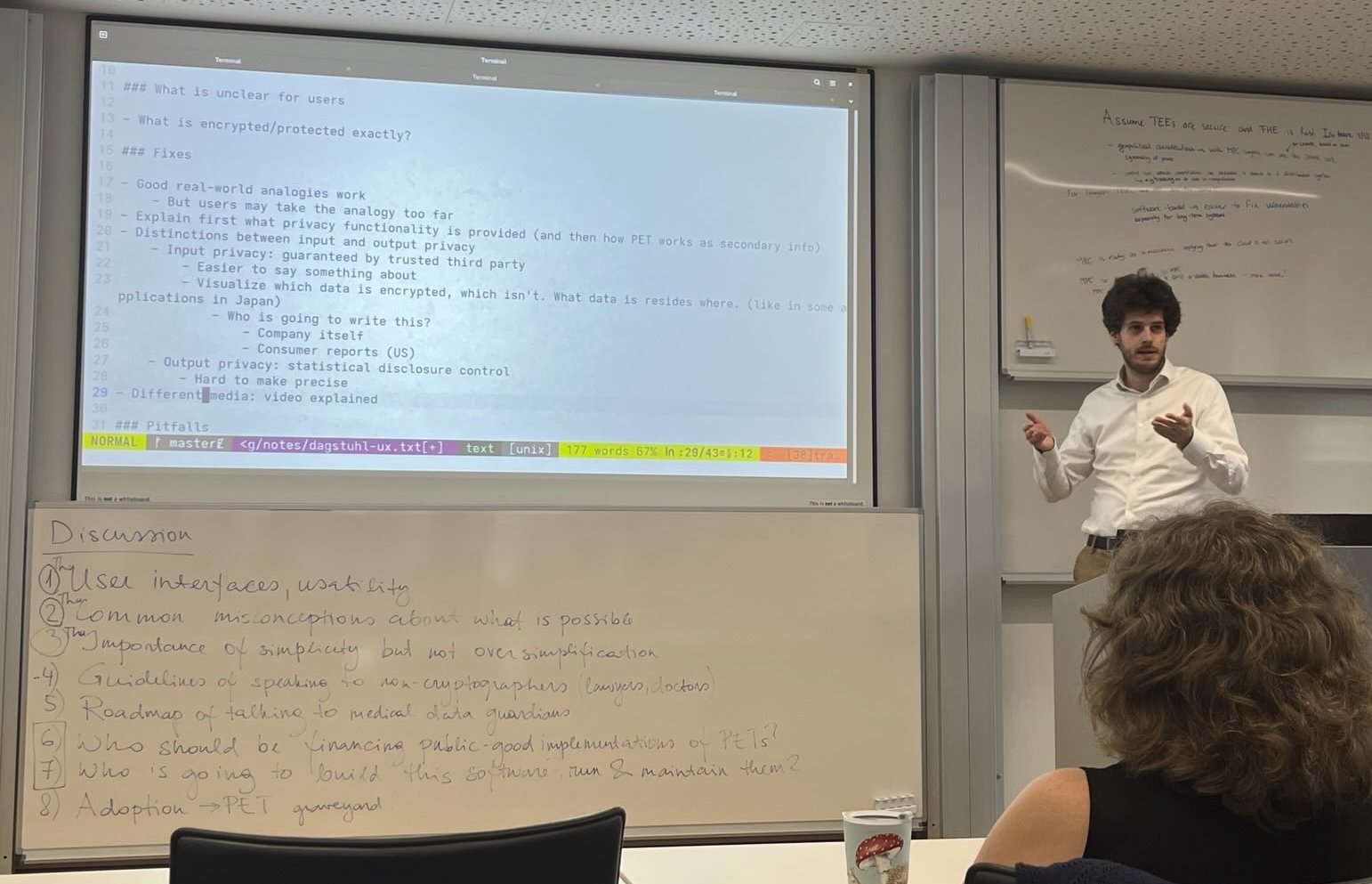 Our colleague Mark Abspoel chairing a discussion.
Our colleague Mark Abspoel chairing a discussion.
Protecting Journalists and Individuals against Totalitarian States
Kasra EdalatNejad, affiliated to Darmstadt University, talked about DatashareNetwork, a service for investigative journalists to search in document collections held by other journalists, without revealing the query and the querier’s identity. The key cryptographic primitive that enables search with these privacy properties is Multi-Set Private Set Intersection (MS-PSI); for more details see the paper (Usenix ‘20, PDF). This research has lead to a system deployed in the real world, Datashare, that is currently in use by the Internation Consortium of Investigative Journalists (ICIJ).
Boya Wang, affiliated to the Max Planck Institute for Security and Privacy (MPI-SP) in Bochum, talked about the use of steganographic techniques to evade digital censorship. Because her work is not published yet, she asked us to not share more information about this work, hence this part is deliberately kept short.
Both researchers originally come from countries where there is no free press, and where censorship is commonplace. I therefore have great admiration for their courage to address these topics via their research work.
MPC and PETs from a GDPR perspective
Meiko Jensen from Karlstad University decided to completely revise the presentation he had prepared, and talk about “MPC and PETs from a GDPR perspective,” in which he shared his perspective on various regulation-related matters that had come up in the room earlier that week.
The question “whether MPC (or PETs) can make data processing anonymous in the context of GDPR” came up several times; a question that we (as Roseman Labs) settled long ago for ourselves and our clients. In a nutshell, our two-fold conviction here is that: a) MPC is a particularly strong form of pseudonymisation, and b) trying to achieve anonymisation is a waste of time and effort if you want to scale a use case internationally, because the DPAs of the various jurisdictions in the EU have strongly different opinions regarding the attainability of anonymisation. We regard MPC as a technical measure in GDPR parlance, namely one that brings value by lowering residual risk (analysed by means of a DPIA) and by simplifying this risk analysis itself, through the clarity provided by the provable guarantees of the cryptographic protocols, about what information is ultimately revealed. Moreover, MPC concretely achieves data minimisation, privacy-by-design and privacy-by-default, and in our MPC proposition, we also achieve purpose binding via the query-approval mechanism.
Preventing the Synthesis of “Forbidden” DNA Molecules
Carsten Baum, from DTU Copenhagen, gave an interesting talk about a large research collaboration project about screening DNA synthesis. Today, you can design a DNA molecule on a computer, and have it synthesized by a synthesis company into a real molecule, and shipped to a postal address within 48 hours. There even exist “benchtop” DNA printers, meaning: a DNA printing machine that fits on a regular desk.
For obvious reasons, it is important that clients of these synthesis companies (or benchtop-printer users), do not print pathogens, such as the Influenza virus. Hence, there is a need to screen the DNA synthesis orders for pathogen-like patterns.
The screening needs to be done against a global up-to-date list of known and emerging hazards. On the other hand, a synthesis company wants to keep the DNA designs, their clients’ intellectual property, confidential. This is where PETs come to the rescue!
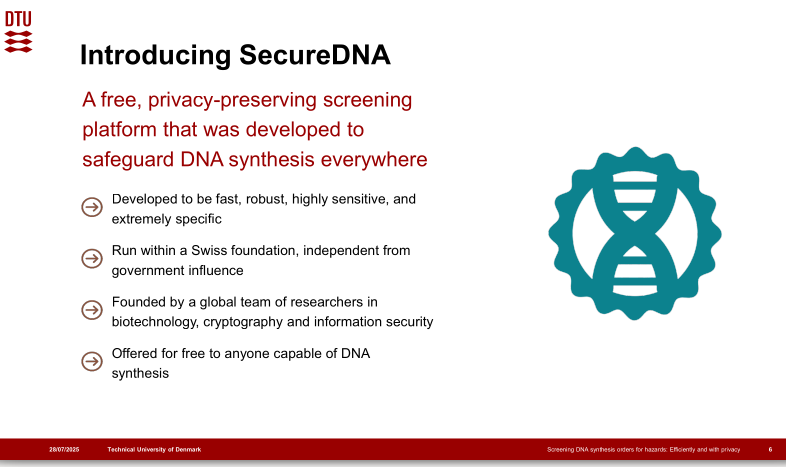 A slide from Carsten Baum’s presentation.
A slide from Carsten Baum’s presentation.
Our Contributions to the Seminar
On Monday, I presented the use case of one of our clients, the Municipality of Rotterdam, about privacy-preserving monitoring in toddlers for developmental delay, for which we were awarded the 2025 Dutch Privacy Awards. After explaining the use case, I digressed into the technical problem of assuring the integrity of web apps to non-technical users. Interestingly, there is an ongoing effort in the W3C lead by Mozilla and Meta, named Web Application Integrity, Consistency and Transparency (WAICT) to address this.
Mark presented our recent work on the Registry, a component for coordinating MPC parties, or, more precisely, a tamper-resistant distributed database component for safely storing public metadata. We can easily fill a separate blogpost with Registry-related content, which we should, actually—some next time, that is!